UNE EXPÉRIENCE INÉGALÉE
GUIDÉE PAR L'INNOVATION
Depuis plus de 60 ans, Mirion Technologies a développé une expertise reconnue dans la conception et la fabrication d'équipements et de solutions pour la détection, la mesure et l'analyse des rayonnements ionisants dans les domaines de l'industrie nucléaire, la défense civile et militaire, la médecine nucléaire, la recherche, l’environnement et autres industries spécialisées.
En savoir plus
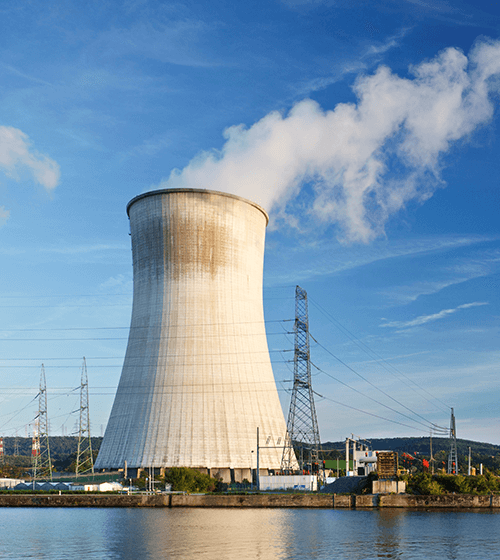
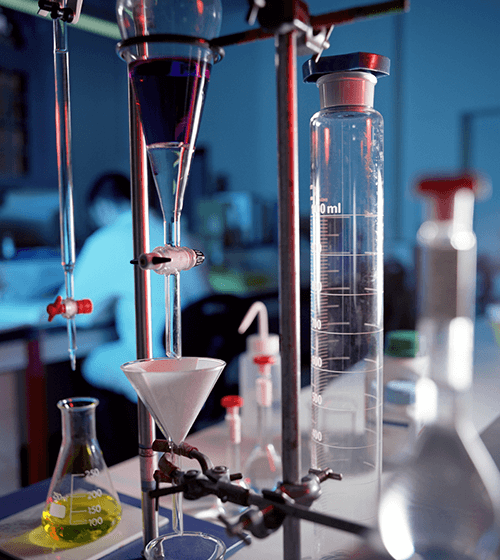
LES DOMAINES D'APPLICATIONS
Sélectionnez votre secteur d'activité et découvrez nos solutions
Aucune vidéo sélectionnée
Sélectionnez un type de vidéo dans la barre latérale.